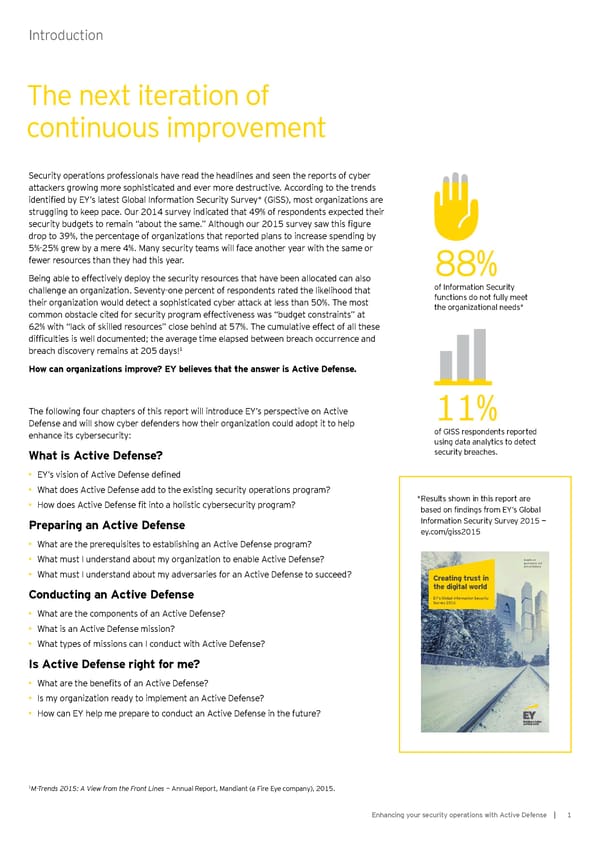
Introdu ction The next iteration of continu ou s improvement S ecu rity operations prof essionals have read the headlines and seen the reports of cy b er attackers grow ing more sophisticated and ever more destru ctive. A ccording to the trends identified by EY’s latest Global Information Security Survey* (GISS), most organizations are stru ggling to keep pace. O u r 2 0 1 4 su rvey indicated that 4 9 % of respondents ex pected their security budgets to remain “about the same.” Although our 2015 survey saw this figure drop to 39%, the percentage of organizations that reported plans to increase spending by 5 % - 2 5 % grew b y a mere 4 % . M any secu rity teams w ill f ace another y ear w ith the same or f ew er resou rces than they had this y ear. 8 8 % B eing ab le to ef f ectively deploy the secu rity resou rces that have b een allocated can also challenge an organization. Seventy-one percent of respondents rated the likelihood that of Inf ormation S ecu rity their organization would detect a sophisticated cyber attack at less than 50%. The most f u nctions do not f u lly meet common ob stacle cited f or secu rity program ef f ectiveness w as “ b u dget constraints” at the organizational needs* 62% with “lack of skilled resources” close behind at 57%. The cumulative effect of all these difficulties is well documented; the average time elapsed between breach occurrence and b reach discovery remains at 2 0 5 day s! 1 H ow can organiz ations im p rov e? E Y bel iev es that the answ er is A ctiv e D efense. The following four chapters of this report will introduce EY’s perspective on Active 1 1 % Defense and will show cyber defenders how their organization could adopt it to help enhance its cy b ersecu rity : of GISS respondents reported u sing data analy tics to detect W hat is A ctiv e D efense? secu rity b reaches. • EY’s vision of Active Defense defined • W hat does A ctive D ef ense add to the ex isting secu rity operations program? • How does Active Defense fit into a holistic cybersecurity program? * Results shown in this report are based on findings from EY’s Global P rep aring an A ctiv e D efense Inf ormation S ecu rity S u rvey 2 0 1 5 — ey . com/ giss2 0 1 5 • W hat are the prereq u isites to estab lishing an A ctive D ef ense program? • What must I understand about my organization to enable Active Defense? Insights on governance, risk and compliance • W hat mu st I u nderstand ab ou t my adversaries f or an A ctive D ef ense to su cceed? Creating trust in Conducting an A ctiv e D efense the digital w orl d E Y ’s G lobal Inf ormation S ecu rity S u rvey 2015 • W hat are the components of an A ctive D ef ense? • W hat is an A ctive D ef ense mission? • W hat ty pes of missions can I condu ct w ith A ctive D ef ense? Is A ctiv e D efense right for m e? • What are the benefits of an Active Defense? • Is my organization ready to implement an Active Defense? • How can EY help me prepare to conduct an Active Defense in the future? 1 M-Trends 2015: A View from the Front Lines — Annual Report, Mandiant (a Fire Eye company), 2015. E nhancing y ou r secu rity operations w ith A ctive Def ense | 1
 Enhancing your Security Operations with Active Defense Page 2 Page 4
Enhancing your Security Operations with Active Defense Page 2 Page 4