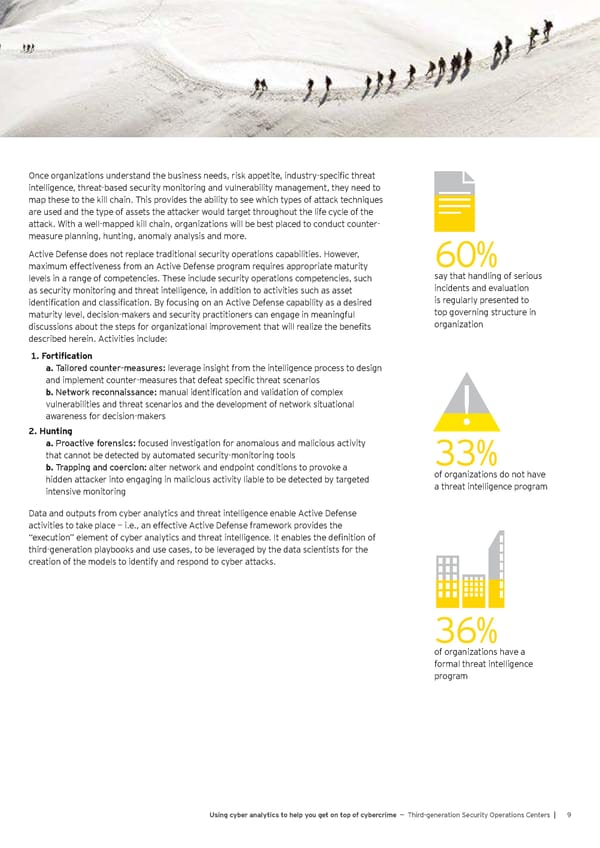
Once organizations understand the business needs, risk appetite, industry-specific threat intelligence, threat-based security monitoring and vulnerability management, they need to map these to the kill chain. This provides the ability to see which types of attack techniques are used and the type of assets the attacker would target throughout the life cycle of the attack. With a well-mapped kill chain, organizations will be best placed to conduct counter- measure planning, hunting, anomaly analysis and more. Active Defense does not replace traditional security operations capabilities. However, 60% maximum effectiveness from an Active Defense program requires appropriate maturity levels in a range of competencies. These include security operations competencies, such say that handling of serious as security monitoring and threat intelligence, in addition to activities such as asset incidents and evaluation identification and classification. By focusing on an Active Defense capability as a desired is regularly presented to maturity level, decision-makers and security practitioners can engage in meaningful top governing structure in discussions about the steps for organizational improvement that will realize the benefits organization described herein. Activities include: 1. Fortification a. Tailored counter-measures: leverage insight from the intelligence process to design and implement counter-measures that defeat specific threat scenarios b. Network reconnaissance: manual identification and validation of complex vulnerabilities and threat scenarios and the development of network situational awareness for decision-makers 2. Hunting a. Proactive forensics: focused investigation for anomalous and malicious activity that cannot be detected by automated security-monitoring tools 33% b. Trapping and coercion: alter network and endpoint conditions to provoke a of organizations do not have hidden attacker into engaging in malicious activity liable to be detected by targeted a threat intelligence program intensive monitoring Data and outputs from cyber analytics and threat intelligence enable Active Defense activities to take place — i.e., an effective Active Defense framework provides the “execution” element of cyber analytics and threat intelligence. It enables the definition of third-generation playbooks and use cases, to be leveraged by the data scientists for the creation of the models to identify and respond to cyber attacks. 36% of organizations have a formal threat intelligence program Using cyber analytics to help you get on top of cybercrime — Third-generation Security Operations Centers | 9
 Using Cyber Analytics to help you get on top of Cybercrime Page 10 Page 12
Using Cyber Analytics to help you get on top of Cybercrime Page 10 Page 12